Tech
Defending Against Wadware: A Comprehensive Guide to Protecting Your Digital Security
Published
4 months agoon
By
admin
1. Introduction to Wadware
Wadware is a type of software that can cause harm to your computer or mobile device. It’s important to understand what wadware is and how it works to protect yourself from potential threats.
Definition and Explanation
Wadware, also known as potentially unwanted programs (PUPs), are software programs that often come bundled with other free software you download from the internet. They may seem harmless at first, but they can secretly collect your personal information, display annoying advertisements, or even damage your device.
Origin and Evolution
Wadware has been around for many years, evolving alongside the internet and technological advancements. It originated as a way for companies to track user behavior and display targeted advertisements. However, it has since grown more sophisticated and can now pose serious threats to your privacy and security.
Differentiation from Adware and Malware
Wadware is often confused with adware and malware, but there are important differences between them. Adware displays unwanted advertisements, while malware is malicious software designed to harm your device or steal your information. Wadware falls somewhere in between, as it may exhibit characteristics of both adware and malware.
2. Understanding Wadware: Types and Characteristics
To effectively protect yourself from wadware, it’s crucial to understand its different types and key characteristics. By knowing how wadware operates, you can better recognize and defend against potential threats.
Classification of Wadware
Wadware comes in various forms, each with its own methods of operation and potential risks. Some common types of wadware include:
- Browser hijackers: These programs take control of your web browser, redirecting you to unwanted websites and displaying intrusive ads.
- Ad injectors: Ad injectors insert additional advertisements into web pages you visit, disrupting your browsing experience and potentially exposing you to malicious content.
- Spyware: Spyware secretly monitors your online activities and collects sensitive information, such as login credentials and credit card numbers, without your consent.
- Keyloggers: Keyloggers record every keystroke you make on your device, allowing attackers to steal your passwords and other confidential data.
Key Features and Functions
While wadware can vary in its specific features and functions, there are some common characteristics that define this type of software:
- Stealthy installation: Wadware often installs itself onto your device without your knowledge or consent, making it difficult to detect and remove.
- Persistent presence: Once installed, wadware can be challenging to remove completely, as it may hide itself within system files or disguise its processes.
- Behavior tracking: Many wadware programs track your online behavior and collect data about your browsing habits, which can be used for targeted advertising or sold to third parties.
- Resource consumption: Some wadware programs consume significant system resources, slowing down your device and affecting its performance.
3. The Risks Posed by Wadware

Wadware can pose significant risks to your privacy, security, and overall digital well-being. It’s essential to be aware of these risks so you can take steps to protect yourself and your devices.
Potential Hazards and Threats
Wadware can expose you to various hazards and threats, including:
- Privacy invasion: Wadware may track your online activities, such as websites visited and search queries, without your consent. This invasion of privacy can lead to the unauthorized collection and misuse of your personal information.
- Identity theft: Some wadware programs are designed to steal sensitive information, such as login credentials, credit card numbers, and social security numbers. This stolen information can be used for identity theft and financial fraud.
- Financial losses: Wadware can lead to financial losses through fraudulent activities, such as unauthorized purchases or draining your bank account. Additionally, wadware-infected devices may require costly repairs or replacements.
- Disruption of services: Wadware can disrupt your online experience by injecting unwanted advertisements, redirecting your web searches, or slowing down your device’s performance. This disruption can be frustrating and time-consuming to deal with.
Legitimacy Concerns
One of the challenges with wadware is determining its legitimacy. While some wadware programs may have legitimate purposes, such as collecting data for marketing research, others may engage in unethical or illegal activities. It’s essential to exercise caution when encountering wadware and to research its reputation and intentions before allowing it access to your device.
Real-life Examples and User Experiences
Numerous real-life examples demonstrate the risks and consequences of wadware infections. Stories of individuals falling victim to identity theft, financial fraud, and other wadware-related crimes serve as sobering reminders of the importance of staying vigilant and protecting yourself against these threats.
4. Impact on Systems and Users
Wadware can have a profound impact on both the systems it infects and the users who encounter it. Understanding these effects is crucial for safeguarding against wadware-related risks and maintaining a secure digital environment.
Effects on Personal Information Security
One of the most significant impacts of wadware is its threat to personal information security. Wadware can collect sensitive data, such as login credentials, financial information, and browsing history, without the user’s knowledge or consent. This compromised information can then be used for identity theft, financial fraud, or other malicious purposes, putting users at risk of significant harm.
Financial Losses and Fraudulent Activities
Wadware-infected systems are also vulnerable to financial losses and fraudulent activities. Attackers can use stolen information to make unauthorized purchases, drain bank accounts, or engage in other fraudulent transactions, resulting in monetary losses for the affected users. Additionally, wadware infections may lead to additional expenses, such as the cost of repairing or replacing compromised devices.
Disruption of Services
Wadware can disrupt the normal operation of systems and services in various ways. For example, it may inject unwanted advertisements into web pages, redirect users to malicious websites, or degrade the performance of infected devices. These disruptions can impair productivity, decrease user satisfaction, and create frustration for affected individuals.
Media Coverage and Public Perception
The impact of wadware is often reflected in media coverage and public perception. High-profile wadware incidents and data breaches frequently make headlines, raising awareness of the risks associated with these threats. Public perception of wadware may influence user behavior and attitudes toward digital security, highlighting the importance of effective prevention and mitigation strategies.
5. How Wadware Operates: Mechanisms and Modes of Infection
Understanding how wadware operates is essential for recognizing and preventing its spread. By familiarizing yourself with the mechanisms and modes of infection used by wadware, you can take proactive steps to protect your devices and personal information.
Infection Routes and Vulnerabilities Exploited
Wadware can infect devices through various routes and exploit vulnerabilities in both software and user behavior. Common infection routes include:
- Bundled software: Wadware often disguises itself as legitimate software and is bundled with free downloads from the internet. Users may inadvertently install wadware alongside desired programs without realizing it.
- Malicious websites: Visiting malicious websites or clicking on suspicious links can expose users to wadware infections. These websites may exploit vulnerabilities in web browsers or use social engineering tactics to trick users into downloading malicious software.
- Email attachments: Wadware may spread through email attachments containing infected files or links to malicious websites. Users who open these attachments or click on links may inadvertently download wadware onto their devices.
Signs and Symptoms of Wadware Presence
Recognizing the signs and symptoms of wadware presence is crucial for early detection and mitigation. Common indicators of wadware infection include:
- Unwanted advertisements: Wadware often displays intrusive advertisements or pop-ups while browsing the internet, even on websites that don’t typically contain ads.
- Browser redirects: Wadware may redirect users to unfamiliar or suspicious websites when attempting to access legitimate web pages.
- Slow performance: Wadware can consume system resources and slow down device performance, causing applications to load slowly or freeze unexpectedly.
- Changes to browser settings: Wadware may modify browser settings, such as the homepage or default search engine, without user consent.
User Awareness and Detection Techniques
User awareness plays a critical role in detecting and preventing wadware infections. By staying vigilant and employing detection techniques such as:
- Regularly scan devices with reputable anti-malware software to detect and remove wadware infections.
- Being cautious when downloading software or clicking on links from unfamiliar sources.
- Keeping software and operating systems up-to-date with the latest security patches and updates to prevent vulnerabilities from being exploited.
6. Protecting Against Wadware Attacks

Protecting yourself against wadware attacks requires a combination of proactive measures and ongoing vigilance. By implementing effective prevention strategies and best practices, you can reduce the risk of wadware infections and safeguard your devices and personal information.
Prevention Strategies and Best Practices
There are several prevention strategies and best practices you can adopt to protect yourself against wadware attacks, including:
- Download software from reputable sources: Only download software from trusted sources, such as official app stores or the websites of reputable developers. Avoid downloading software from unfamiliar or unverified sources, as they may contain wadware or other malicious software.
- Read user reviews and ratings: Before downloading software, read user reviews and ratings to gauge its reputation and reliability. Look for any complaints or reports of wadware infections or other issues that could indicate potential risks.
- Be cautious with email attachments and links: Exercise caution when opening email attachments or clicking on links, especially if they come from unknown or suspicious senders. Be wary of unsolicited emails and avoid downloading attachments or clicking on links unless you trust the source.
- Use security software: Install reputable anti-malware software on your devices and keep it up-to-date with the latest definitions and security patches. Regularly scan your devices for wadware and other malware infections to detect and remove any threats.
- Keep software and operating systems updated: Ensure that your software and operating systems are up-to-date with the latest security patches and updates. Vulnerabilities in outdated software can be exploited by wadware and other malware to infect your devices.
- Enable security features: Take advantage of built-in security features and settings on your devices and software applications. Enable firewalls, pop-up blockers, and other security features to help protect against wadware attacks and other security threats.
Importance of Regular Software Updates
Regularly updating your software and operating systems is crucial for protecting against wadware attacks. Software updates often include security patches and fixes that address known vulnerabilities exploited by wadware and other malware. By keeping your software up-to-date, you can reduce the risk of wadware infections and ensure that your devices remain secure.
7. Detecting and Removing Wadware
Detecting and removing wadware from your devices is essential for maintaining their security and protecting your personal information. By following a step-by-step guide and utilizing effective anti-malware software, you can identify and eliminate wadware infections before they cause further harm.
Step-by-Step Guide for Users
Follow these steps to detect and remove wadware from your devices:
Step 1: Identify and Assess the Threat
- Use reputable anti-malware software to scan your device for wadware infections.
- Take note of any suspicious files, programs, or behavior that may indicate the presence of wadware.
Step 2: Back Up Your Important Files
- Before attempting to remove wadware, back up your important files and data to ensure they are not lost in the process.
- Store your backups on an external hard drive, cloud storage service, or other secure location.
Step 3: Use Anti-Malware Software to Remove Wadware
- Run a full system scan with your anti-malware software to detect and remove wadware infections.
- Follow the prompts to quarantine or delete any identified threats from your device.
- Consider using additional anti-malware tools or seeking professional assistance if the infection persists or is particularly severe.
Step 4: Update Your Operating System and Software
- After removing wadware infections, ensure that your operating system and software are up-to-date with the latest security patches and updates.
- Regularly check for updates and install them as soon as they become available to protect against future wadware attacks.
Prevention Tips to Avoid Future Wadware Infections
To prevent future wadware infections, consider implementing the following prevention tips:
- Be cautious when downloading software from the internet, and only download from reputable sources.
- Keep your anti-malware software up-to-date and regularly scan your device for threats.
- Avoid clicking on suspicious links or email attachments, and be wary of unsolicited emails.
- Enable security features on your devices and software applications, such as firewalls and pop-up blockers.
- Stay informed about the latest wadware threats and security best practices to protect yourself and your devices effectively.
8. Future Trends and Outlook
Understanding the future trends and outlook for wadware is crucial for staying ahead of emerging threats and adapting security measures accordingly. By anticipating changes in wadware development and evolving countermeasures, individuals and organizations can better protect themselves against future wadware-related risks.
Predictions for Wadware Development
As technology continues to advance, wadware is likely to evolve in response to changing trends and developments. Some predictions for wadware development include:
- Increased sophistication: Wadware may become more sophisticated in its tactics and techniques, making it harder to detect and remove.
- Targeted attacks: Wadware may increasingly target specific individuals, organizations, or industries, tailoring its attacks to exploit vulnerabilities and maximize impact.
- Cross-platform threats: With the proliferation of interconnected devices and platforms, wadware may target multiple operating systems and devices to maximize its reach and effectiveness.
- Integration with other threats: Wadware may be integrated with other types of malware, such as ransomware or banking trojans, to create more complex and dangerous cyber threats.
Emerging Threats and Evolving Countermeasures
As wadware continues to evolve, so too must the countermeasures used to defend against it. Some emerging threats and evolving countermeasures include:
- Behavioral analysis: Anti-malware software may employ advanced behavioral analysis techniques to detect and block wadware based on its actions and behavior, rather than relying solely on signature-based detection methods.
- Cloud-based security solutions: Cloud-based security solutions may provide real-time threat intelligence and analysis, allowing organizations to detect and respond to wadware attacks more effectively.
- Enhanced user education and awareness: Educating users about the risks of wadware and how to protect themselves against it is crucial for preventing infections and minimizing the impact of wadware-related threats.
- Collaboration and information sharing: Collaboration between security researchers, industry partners, and law enforcement agencies can help identify and mitigate wadware threats more quickly and effectively.
Long-term Implications for Cybersecurity
The long-term implications of wadware for cybersecurity are significant and far-reaching. As wadware continues to evolve and adapt to changing technology and security landscapes, it poses ongoing challenges for individuals, organizations, and society as a whole. However, by staying informed, adopting best practices, and leveraging advanced security solutions, we can mitigate the impact of wadware and safeguard against future threats.
9. Conclusion: Navigating the Digital Landscape Safely
In conclusion, navigating the digital landscape safely requires awareness, vigilance, and proactive measures to protect against wadware and other cybersecurity threats. By summarizing key points and emphasizing the importance of ongoing security practices, we can reinforce the importance of digital security and empower individuals and organizations to stay safe online.
Summary of Key Points
Throughout this article, we have explored the dangers of wadware, including its impact on personal information security, financial losses, and disruption of services. We have discussed how wadware operates, its various types and characteristics, and the steps individuals can take to detect and remove wadware infections from their devices. Additionally, we have examined future trends and outlook for wadware, highlighting the need for ongoing vigilance and adaptation to evolving threats.
Encouragement for Vigilance and Proactive Security Measures
As technology continues to advance and threats evolve, it is essential to remain vigilant and proactive in protecting against wadware and other cybersecurity risks. By following best practices such as downloading software from reputable sources, keeping software up-to-date, and using anti-malware software, individuals can reduce the risk of wadware infections and safeguard their personal information and devices.
Call to Action for Continued Awareness and Education
Finally, we encourage readers to continue educating themselves about wadware and other cybersecurity threats, staying informed about the latest developments and best practices for staying safe online. By prioritizing digital security and taking proactive measures to protect against wadware, individuals and organizations can navigate the digital landscape safely and securely.
10. FAQs on Wadware
In this section, we address frequently asked questions (FAQs) about wadware to provide clarity and guidance on common concerns and inquiries related to this type of cybersecurity threat.
What is Wadware, and How is it Different from Adware and Malware?
Wadware, also known as potentially unwanted programs (PUPs), is software that can compromise your privacy and security by displaying unwanted advertisements, tracking your online activities, or collecting sensitive information without your consent. While wadware shares similarities with adware and malware, it differs in its intentions and behaviors. Adware primarily displays advertisements, while malware is malicious software designed to harm your device or steal your information. Wadware falls somewhere in between, as it may exhibit characteristics of both adware and malware.
How Can I Protect My Device from Wadware?
To protect your device from wadware, follow these tips:
- Download software from reputable sources.
- Use anti-malware software and keep it up-to-date.
- Be cautious with email attachments and links.
- Enable security features on your devices and software applications.
- Stay informed about the latest wadware threats and security best practices.
Is Wadware Legal, and What Are the Implications?
The legality of wadware depends on its behavior and intentions. While some wadware programs may have legitimate purposes, such as collecting data for marketing research, others may engage in unethical or illegal activities. Wadware that violates user privacy or engages in malicious behavior may be subject to legal action and penalties.
How Can I Recognize Wadware on My System?
You can recognize wadware on your system by looking for signs and symptoms such as:
- Unwanted advertisements or pop-ups.
- Browser redirects to unfamiliar or suspicious websites.
- Slow device performance.
- Changes to browser settings without your consent.
What Does the Future Hold for Wadware Threats?
The future of wadware threats is likely to involve increased sophistication, targeted attacks, and integration with other types of malware. As technology continues to advance, wadware may evolve to exploit new vulnerabilities and adapt to changing security landscapes. Staying informed about emerging threats and evolving countermeasures is essential for protecting against future wadware-related risks.
You may Also Read: Minus Two
Tech
The creativity behind editor Benjamin Tech Guru Keezy.co
Published
4 days agoon
July 23, 2024By
admin
editor Benjamin Tech Guru Keezy.co, In this technology-obsessed world, there are many ways to improve your mind using different technologies. Technology has become an integral part of our daily lives, enriching our personal lives and helping us in many ways. In today’s blog from webtechneed.com we will discuss an innovative and revolutionary platform that is changing the way we interact with technology – editor Benjamin Tech Guru Keezy.co. With many innovative features, Keezy.co offers users a great experience that sets it apart from traditional apps.
But before we learn about this amazing technology, let’s first explore Benjamin’s vision. If you haven’t heard about him yet, you’re in for a surprise. Benjamin is the brains behind Keezy.co, a pioneering technology platform that has become an industry leader. With a special talent for innovation and a passion for technology, Benjamin has transformed Keezy.co into a beacon of tech magic. Stay with us as we explore all the relevant information about Tech Guru Keezy.co.
In this guide we try to get answers to the most frequently asked questions about editor Benjamin Tech Guru Keezy.co. Check the next section.
Beginnings
Every tech wizard has a backstory, and editor Benjamin Tech Guru Keezy.co story is no exception. He grew up in a family where he received a proper education. He was particularly interested in what he was studying. His passion for experimenting with devices and exploring the digital world shows his blind interest in technology. His future projects were made possible by this passion. His ongoing commitment laid the foundation for Keezy.co, which would spread true vision in the technology industry. Let’s talk about the birth of keezy.co.
The birth of Keezy.co
Editor Benjamin came up with the idea to create Keezy.co, a website that offers many cutting-edge skills for computer professionals while simplifying technology for customers in general. Founded in 2015, Keezy.co instantly became known for its unique combination of powerful features and user-friendly design. Benjamin’s quick problem-solving skills make him an invaluable member of the team.
Industry executives, including those at keezy.co, noticed his efforts, recognized his potential and made him a job offer. The real goal of the platform is to give anyone with technical skills the opportunity to enjoy and benefit from technology. Benjamin enjoys experimenting with new technologies and sharing his opinions with his audience, whether it’s about cutting-edge smart home devices or the latest smartphones.
Editor Benjamin Tech Guru Keezy.co’s journey is marked by great accomplishments. The platform has consistently exceeded expectations.
Benjamin believes in giving back to the community. Keezy.co is actively involved in several technology industries, collaborates with other organizations and participates in industry events. These efforts not only improve the platform’s reputation, but also contribute to the broader technology ecosystem.
Innovative methods
editor Benjamin Tech Guru Keezy.co What sets Keezy.co apart from the rest? It is Benjamin’s innovative way of thinking. Keezy.co offers unique features that appeal to a wide range of users, from tech novices to professionals. The role Benjamin played in driving these innovations cannot be overstated. His vision and unique approach became instrumental in shaping the platform.
editor Benjamin Tech Guru Keezy.co What is the technical interface behind Keezy.co? Keezy.co usually has the latest technology to provide great technical solutions. Be it the stunning user interface or the powerful back-end system, this premium technology stands out in this competitive world of technology.
Amazing technical features:
Keezy.co is changing the industry and is more than just a technology platform. Keezy.co offers a great user experience thanks to its modern features.
It is a kind of innovation designed for beginners and professionals. Its user-friendly interface is one of its most notable features. With just a few clicks, anyone can easily create and edit content, making music production accessible to everyone.
editor Benjamin Tech Guru Keezy.co An added bonus is the huge collection of sounds and effects available to you. Users have many options to express their creativity, including drums, voices, and synthesizers.
In addition, this platform has collaborative features that allow users to communicate with each other instantly – improving the platform’s community profile.
Keezy.co Team
editor Benjamin Tech Guru Keezy.co Behind every successful platform is a strong team. Benjamin understands this well. Building a qualified team was one of his top priorities. The Keezy.co team consists of experienced professionals who share Benjamin’s passion for technology. Team members play an important role in keeping the platform unique.
User experience
Benjamin’s worldview is user-centric. Keezy.co was created with the user in mind. It ensures everyone has a great experience. There are positive reviews from customers highlighting the platform’s reliability and ease of use. This focus on user experience is a testament to Benjamin’s commitment.
User success stories and partnerships with large companies
Discover Editor Benjamin Tech Guru’s world of Keezy.co, where success stories happen every day. Benjamin’s innovative platform provides users from all over the world with the highest level of creativity and efficiency. Keezy.co is making a difference in the digital sector.
Large companies have also taken notice and partnered with Keezy.co to improve their own offerings. Amazing partnerships are now possible thanks to the amazing features of this new tool. Users now have access to amazing features and functionality that also improve their creative processes.
The future vision of Keezy.co
What is Keezy.co’s vision for the future? Benjamin has big ideas. As Keezy.co continues to push the boundaries of the tech industry, the future looks brighter than ever.
editor Benjamin Tech Guru Keezy.co The Keezy.co team is constantly working on improvements and new features to improve the user experience and keep up with industry trends. Users can expect quality from Keezy.co in everything from enhanced audio conversion features to other creative applications.
editor Benjamin Tech Guru Keezy.co In addition to expanding its existing features, Keezy.co is also exploring partnerships with major companies in the technology and music sectors.
Keezy.co, which prioritizes innovation and customer satisfaction, can bring about a major transformation in the technology sector.
Challenges and how to overcome them
No journey is successful without facing challenges. Benjamin and his team also faced many challenges. From technical problems to market competition, they have seen it all. However, her stability and problem-solving skills turned these challenges into opportunities for growth.
Conclusion
Without editor Benjamin Tech Guru Keezy.co a doubt, Editor Benjamin’s power will continue to transform the tech industry for years to come, especially with Keezy.co leading the way. With Keezy.co, editor Benjamin’s creative work has completely changed the tech industry. Editor Benjamin Tech Guru Keezy.co’s unique features showcase the diversity of people’s use of technology. User success stories from well-known companies show the impact of this platform.
Tech
RJCNrj: Innovating the Renewable Energy Landscape
Published
1 week agoon
July 17, 2024By
robert log
Origins and Mission
RJCNrj was founded by a group of environmental enthusiasts and engineers with a shared vision of creating a sustainable future through renewable energy. The mission of RJCNrj is to develop and implement cutting-edge renewable energy technologies that reduce carbon emissions, enhance energy efficiency, and provide reliable, clean power to communities worldwide. The founders believed that through innovation and dedication, they could address the global energy crisis and combat climate change.
Core Technologies
RJCNrj’s success is built on a foundation of advanced technologies that drive its innovative solutions. These core technologies include:
1. Solar Power
RJCNrj harnesses the power of the sun through state-of-the-art photovoltaic (PV) technology. The company has developed high-efficiency solar panels that convert sunlight into electricity with minimal energy loss. These panels are designed for both residential and commercial applications, providing a versatile solution for various energy needs.

2. Wind Energy
Wind energy is another cornerstone of RJCNrj’s renewable energy portfolio. The company has invested in the development of advanced wind turbines that maximize energy output while minimizing environmental impact. These turbines are equipped with cutting-edge sensors and control systems that optimize performance based on real-time wind conditions.
3. Energy Storage
To address the intermittent nature of renewable energy sources, RJCNrj has developed robust energy storage solutions. These include advanced battery systems that store excess energy generated during peak production times for use during periods of low generation. This ensures a consistent and reliable power supply, even when the sun isn’t shining or the wind isn’t blowing.
4. Smart Grid Technology
RJCNrj’s smart grid technology integrates renewable energy sources with traditional power grids, enabling efficient distribution and management of electricity. Smart grids use real-time data and advanced analytics to balance supply and demand, reduce energy waste, and enhance grid stability.
Key Innovations
RJCNrj has introduced several groundbreaking innovations that distinguish it from other players in the renewable energy sector. Some of the most notable include:
1. Floating Solar Farms
Recognizing the limitations of land-based solar installations, RJCNrj has pioneered the development of floating solar farms. These installations are deployed on bodies of water, such as lakes and reservoirs, making use of otherwise underutilized space. Floating solar farms have several advantages, including reduced land use, improved energy efficiency due to cooling effects from the water, and minimized environmental impact.
2. Hybrid Energy Systems
RJCNrj has developed hybrid energy systems that combine multiple renewable energy sources, such as solar and wind, with energy storage. These systems offer greater reliability and efficiency by leveraging the complementary nature of different energy sources. For example, when solar power is low, wind energy can compensate, and vice versa.
3. Advanced Wind Turbine Design

The company has also made significant strides in wind turbine technology. RJCNrj’s turbines feature innovative blade designs and lightweight materials that enhance energy capture and reduce mechanical stress. Additionally, these turbines are equipped with smart sensors that monitor and adjust performance in real-time, ensuring optimal efficiency.
4. Community Energy Projects
RJCNrj is committed to empowering local communities through renewable energy projects. The company partners with municipalities and local organizations to develop community solar and wind projects that provide clean energy at affordable rates. These projects not only reduce carbon footprints but also create jobs and promote economic growth in the regions they serve.
Applications and Impact
The versatility of RJCNrj’s solutions makes them applicable across various sectors, each benefiting from the company’s innovative approach to renewable energy. Some of the most impactful applications include:
1. Residential Energy Solutions
RJCNrj offers a range of renewable energy solutions for residential customers. Homeowners can install solar panels and energy storage systems to generate and store their own electricity, reducing reliance on traditional power grids and lowering energy bills. The company also provides smart home integration, allowing users to monitor and control their energy usage through mobile apps.
2. Commercial and Industrial Energy
For commercial and industrial clients, RJCNrj provides customized renewable energy systems tailored to their specific needs. These solutions help businesses reduce operational costs, achieve sustainability goals, and enhance energy security. RJCNrj’s energy management systems also offer real-time monitoring and analytics, enabling businesses to optimize their energy usage.
3. Utility-Scale Projects
RJCNrj is a major player in utility-scale renewable energy projects. The company designs, constructs, and operates large-scale solar and wind farms that supply clean energy to power grids. These projects significantly reduce carbon emissions and contribute to national and global renewable energy targets.
4. Rural Electrification
In many parts of the world, access to electricity remains a challenge. RJCNrj is addressing this issue through rural electrification projects that bring renewable energy to remote and underserved communities. These projects provide reliable and sustainable power, improving quality of life and enabling economic development.
Challenges and Future Outlook
Despite its significant achievements, RJCNrj faces several challenges that must be addressed to ensure its continued growth and success. These challenges include:
1. Regulatory Hurdles
Navigating the complex regulatory landscape of the energy sector can be challenging. RJCNrj must work closely with governments and regulatory bodies to ensure compliance with local and international standards while advocating for policies that support renewable energy development.
2. Grid Integration
Integrating renewable energy sources into existing power grids requires careful planning and coordination. RJCNrj must address technical challenges such as grid stability, energy storage, and demand management to ensure a seamless transition to renewable energy.
3. Cost Competitiveness
While the cost of renewable energy has decreased significantly, it still faces competition from traditional energy sources. RJCNrj is focused on driving down costs through technological innovation, economies of scale, and efficient project management.
Despite these challenges, the future of RJCNrj looks promising. The company’s dedication to innovation, sustainability, and community empowerment positions it as a leader in the renewable energy sector. As technology continues to evolve, RJCNrj is poised to play a pivotal role in shaping the future of energy production and consumption.
Conclusion
RJCNrj stands at the forefront of the renewable energy revolution, driving significant advancements in solar, wind, and energy storage technologies. By leveraging cutting-edge technologies and innovative solutions, the company is transforming the way energy is produced, distributed, and consumed. The impact of RJCNrj’s innovations is evident across various sectors, from residential and commercial applications to utility-scale projects and rural electrification. As the company continues to navigate challenges and explore new opportunities, its commitment to excellence and sustainability ensures a bright future for renewable energy. RJCNrj’s journey is a testament to the power of technology in creating a greener, more sustainable world, and its contributions will undoubtedly leave a lasting impact on the global energy landscape.
Tech
Discovering Durostech: The Ultimate Guide to Tech Evolution
Published
2 weeks agoon
July 10, 2024By
robert log
A Brief History of Durostech
Durostech was founded in the early 2000s by a group of engineers who shared a common vision: to create technology that not only meets the needs of today but anticipates the demands of tomorrow. Starting as a small startup, Durostech quickly gained traction with its innovative solutions in software development, hardware manufacturing, and digital services.
Pioneering Innovations
Software Solutions
One of Durostch’s significant contributions to the tech world is its robust software solutions. The company has developed a range of applications that cater to various industries, from healthcare to finance. Their software is known for its user-friendly interfaces, high security, and seamless integration with existing systems.

Hardware Advancements
Durosteh didn’t stop at software. They ventured into the hardware realm, creating devices that are not only powerful but also sustainable. Their eco-friendly approach to manufacturing has set a new standard in the industry, proving that performance and sustainability can go hand in hand.
Digital Services
In the age of digital transformation, Durostech offers services that help businesses transition smoothly into the digital age. From cloud computing to cybersecurity, their comprehensive suite of digital services ensures that companies are well-equipped to handle the challenges of modern technology.
The Impact on Various Industries
Healthcare
In healthcare, Durostech has revolutionized patient care with its advanced medical software and devices. Their innovations have made it possible for doctors to diagnose and treat patients more accurately and efficiently.
Finance
For the finance sector, Durostech’s secure and reliable software solutions have enhanced transaction processing and data management. Their technology has streamlined operations, reduced fraud, and improved customer experiences.One of Drostech’s significant contributions to the tech world is its robust software solutions. The company has developed a range of applications that cater to various industries, from healthcare to finance. Their software is known for its user-friendly interfaces, high security, and seamless integration with existing systems.
Education
Durostech’s contributions to education technology have made learning more accessible and engaging. Their e-learning platforms and tools have transformed traditional classrooms, offering students a more interactive and personalized educational experience.
The Future of Durostech
As we look to the future, Durostech is poised to continue its trajectory of innovation and growth. The company’s commitment to research and development ensures that it will remain at the forefront of technological advancements.In the ever-evolving world of technology, staying ahead of the curve can feel like a full-time job. With every new advancement, our lives become more interconnected, efficient, and occasionally, a bit more complicated. Enter Durostech, a company that’s not just riding the tech wave but is one of the key players shaping its direction. This guide will walk you through the journey of Durosech, exploring its impact on the tech industry and what it means for the future.

Emerging Technologies
Durostech is already making strides in emerging technologies such as artificial intelligence, machine learning, and quantum computing. These advancements promise to further revolutionize industries and improve our daily lives in ways we can only begin to imagine.
Global Expansion
With a presence in numerous countries, Durosteh is set on expanding its global footprint. By entering new markets and forging strategic partnerships, the company aims to bring its innovative solutions to a broader audience.
Conclusion
Discovering Durostech is like opening a door to the future of technology. Their contributions to software, hardware, and digital services have made a significant impact across various industries, and their commitment to innovation promises even greater advancements ahead. Whether you’re a tech enthusiast or just someone looking to stay informed about the latest trends, keeping an eye on Durostech will undoubtedly be worth your while.
Trending
-

 Business7 months ago
Business7 months agoQuantity TBD on Amazon: €ководство
-

 Business3 months ago
Business3 months agoIntegremos: Weaving Together the Fabric of Connection
-

 Tech8 months ago
Tech8 months agoDesgrabador
-

 Business8 months ago
Business8 months agoGetting Started With Hqpotner
-

 News7 months ago
News7 months agoWTOV Channel 9 Revealed: The Untold Stories You Never Knew
-

 News8 months ago
News8 months agoHow To Wear Brıston
-

 Blog8 months ago
Blog8 months agoAmerican Express Work from Home Jobs
-
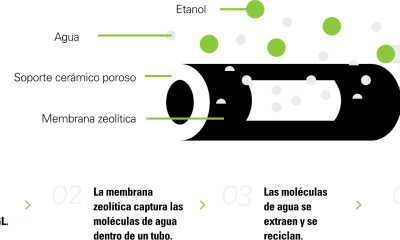
 News8 months ago
News8 months agoWhat Is Zeolítica?


